In crypto, particularly in Bitcoin, one of the most frequently asked question is, "How do I know that nobody else is using the same seed phrase as me?" or "Can You Guess A Bitcoin Private Key"?
Addressing questions like this requires a deep dive into the intricacies of a fundamental concept behind the security of the private key, a number that's used to verify transactions and prove ownership of a blockchain address.
| Emoji and Term | Definition |
|---|---|
| 🔐 Bitcoin Private Key | A 256-bit number granting Bitcoin ownership. Its generation involves immense possibilities, thwarting guesses. |
| 💾 256-bit number | A numerical value with 256 binary digits, widely used in cryptography to represent strong security keys. |
| 📊 Entropy | Crucial randomness source for secure keys. Insecure entropy undermines Bitcoin key security. |
| 🧠 Seed Phrase | Series of words creating deterministic private keys. Poorly generated phrases can compromise security. |
| 🖥️ Quantum Computing | Advanced computing with qubits, potentially threatening cryptographic systems like Bitcoin's private keys. |
Before starting, if you're interested in understanding public-key cryptography, particularly the concepts of private and public keys, you can find more information by following the link provided below.
The 256-bit Number
At the core of Bitcoin's security infrastructure lies the private key – a 256-bit number, or 2^256 in mathematical terms. This value is arrived at by multiplying the number 2 by itself a staggering 256 times.
While this exponential nature might confound our human faculties, let's break it down into something more tangible. Half of 2^256 isn't 2^128, as intuition might suggest, but rather 2^255. To put this number into perspective, 2^256 can be expressed as a decimal figure: 10^77, which consists of the digit 1 followed by a whopping 77 zeros.
How Big Is 10^77?
Visualizing the magnitude of 10^77 is a challenge in itself. Consider the grains of sand on Earth – estimated to range between 10^16 and 10^20. Even more astonishing, a single grain of sand houses about 10^20 molecules of silica. If we multiply these two numbers together, we get 10^40. Imagine if all the grains of sand on every beach and in every desert on ten planets made of sand were considered – that sum would be a colossal 10^41.
Venturing further, let's examine the Milky Way galaxy, containing around 100 billion stars or 10^11 stars. Imagine every single grain of sand across all these planets made of sand, multiplied by the number of stars – this results in an astronomical 10^52.
Expanding our cosmic perspective to the entire observable universe, comprising roughly a hundred billion galaxies, we reach a figure of 10^63. To put it succinctly, this is an astonishingly gargantuan number, beyond the grasp of human intuition.
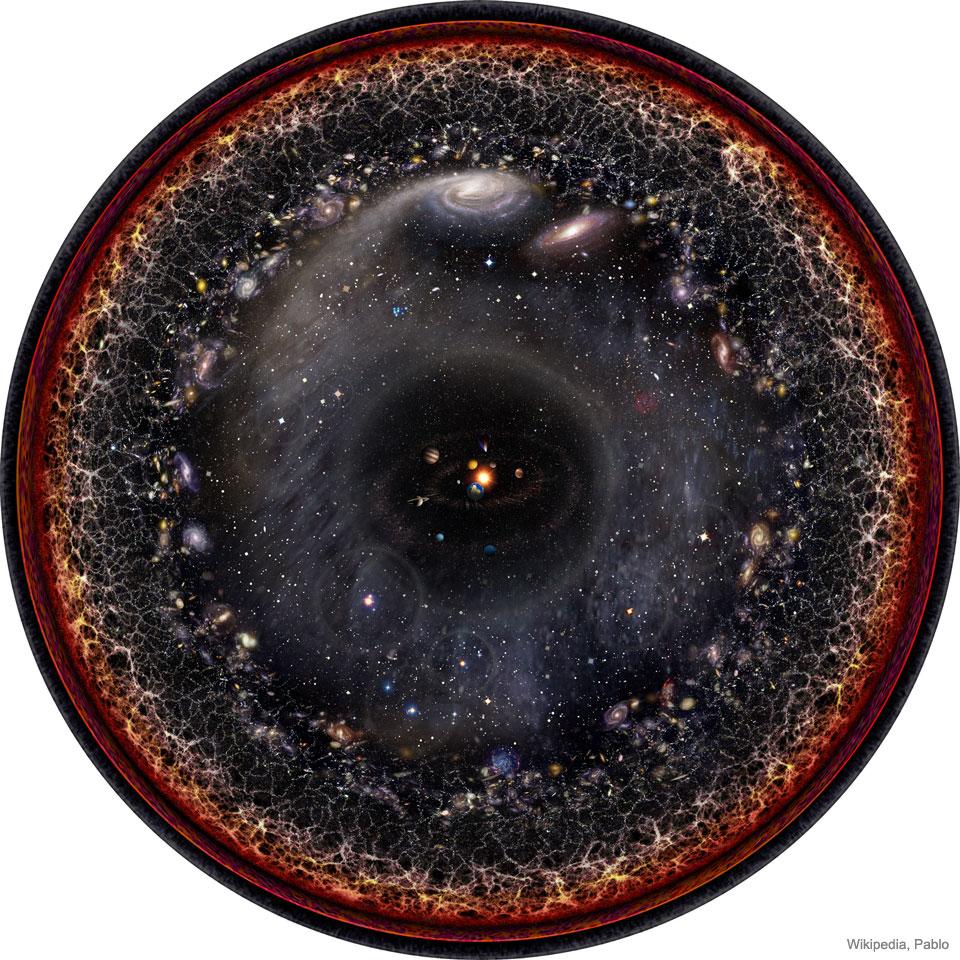
In the field of astrophysics, the "Eddington number" (NEdd) signifies the count of atoms in the observable universe. This expanse spans 13.8 billion light-years and encapsulates all matter within the cone of space-time that is observable to us. Astonishingly, all the atoms in this vast universe sum up to approximately 10^77, a figure that aligns uncannily with the estimates for NEdd – around 10^80.
Remarkably, 10^77 happens to be both the central estimate of NEdd and the maximum number of conceivable bitcoin private keys. To put it in perspective, this number signifies that each atom in the entire observable universe, spanning over a hundred billion galaxies, could theoretically possess its own unique bitcoin private key.
In the end, the notion of guessing a bitcoin private key becomes almost impossible for the human brain. Picking a specific atom from the countless atoms in the universe mirrors the improbability of guessing a private key. The profound uniqueness of these keys is a testament to the cryptographic robustness that underpins the security of Bitcoin, ensuring the safeguarding of digital assets in cyberspace.
Practical example

To comprehend the astonishing unlikelihood of guessing a Bitcoin private key, there is an online tool known as keys.lol. This website works as a random key generator, automatically verifying the balance of each generated wallet thanks to the connection to a blockchain explorer.
Wallets holding a balance are visually highlighted in green. On the other hand, wallets that were previously utilized but now stand empty transition to a yellow hue. Wallets that have never been utilized are distinctly marked in red.
Attempting to stumble upon a wallet containing some BTC through this method is a feat bordering on impossibility, even if one were to dedicate an entire lifetime in front of the computer, incessantly refreshing the page. The exploration of this concept can be experienced firsthand by using the tool itself for a few hours.
The Birthday Paradox and Bitcoin Private Keys
The Birthday Paradox is a well-known probability phenomenon that can help us understand the likelihood of two people sharing the same birthday in a group. However, its application goes beyond birthdays and can shed light on the security of Bitcoin private keys.
Imagine generating a massive number of Bitcoin private keys, each corresponding to a unique wallet. The question arises: How many keys need to be generated before the likelihood of a key collision (two or more keys being the same) becomes statistically significant?
The probabilities for a collision, often referred to as a birthday attack, can be calculated using the formula:
p(g, t) ≈ g^2 / (2t)
Where:
- g: Number of generated keys
- t: Total number of possible keys
Let's break this down with an example. If we have already generated 1 billion keys (g = 10^9) and there are approximately 1 followed by 77 zeros possible keys (t = 10^77), the probability of a collision is an incredibly small number: approximately 5*10^-60. This probability is almost negligible.
When we consider a larger number, say g = 3*10^38 (which is a bit under 50% of the square root of 10^77), the probability of a collision becomes around 0.45. In other words, when we generate keys to this extent, there's about a 50% chance of encountering a collision.
To put this in perspective, imagine a scenario where there are 10 billion people on Earth, and each person generates keys at an astonishing rate of 31.72 billion billion billion keys. Even then, the chance of a key collision would only be as likely as a coin flip.
While the mathematical probabilities provided by the Birthday Paradox show that generating a significant number of identical private keys is unlikely, it's important to note that the security of Bitcoin private keys also depends on various factors, including the quality of the random number generation process and the cryptographic mechanisms in place. Despite the complex math involved, the Bitcoin ecosystem employs strong security measures to safeguard private keys and maintain the integrity of the network.
How Do I Know That Nobody Is Using The Same Seed Phrase / Private Key As Me?
Ensuring the uniqueness of one's seed phrase and private key involves more than just taking in consideration the huge number of potential combinations. Although the inner workings of these mathematical computations are important, they don't entirely address the critical query: "What is the likelihood that two individuals will coincidentally choose the same seed phrase?"
This matter goes deeper into the implementation of the seed generation process within wallets, irrespective of whether they are hardware or software-based. A key concern arises when a wallet possesses a poorly executed or, worse yet, maliciously designed seed generation function. In such instances, the resulting seedphrase (and hence, private key) might not exhibit the expected randomness.
In essence, blindly entrusting a wallet's automatic seed generation procedure without contributing and validating personal entropy can lead to an inability to determine the answer to the aforementioned question until it's already too late.
Fortunately, there are hardware wallets available that offer the option to input and validate entropy while also maintaining a high degree of transparency through their 100% open-source auditable nature. The next section will delve further into one of these hardware wallets and its distinctive attributes.
Should I Generate My Private Key With 12 or 24 words?
As previously noted, a private key is generated by selecting a random number between 1 and just under 2^256, a colossal number with over 115 quattuorvigintillion possibilities. This number is chosen using mechanisms like random number generators to ensure true randomness, critical for robust security. Through cryptographic processes, this number is translated into public keys and addresses that facilitate transactions.
Seed phrases, introduced in 2013, have simplified the process of setting up and restoring wallets easily, without having to deal with complex private keys but with a serious of much more easy to write (and even remember) words.
These phrases, consisting of a sequence of words, provide determinism in generating private keys. The industry norm is a minimum of 12 words, though it can extend to 24 words. Despite the initial inclination to opt for the maximum length, concerns arise regarding the balance between security and usability.
Attack types
For an attacker to compromise private keys or seed phrases, two primary avenues exist:
- Brute-Force Attack: This involves an attacker repeatedly guessing the correct seed phrase. With just a 12-word seed phrase (considered the industry standard), there are 2^128 potential combinations, making it practically impossible to guess correctly within a reasonable timeframe.
- Solving the Elliptic Curve Discrete Logarithm Problem (ECDLP): This attack involves trying to reverse engineer a private key from a given public key (Bitcoin address). Bitcoin uses a 256-bit elliptic curve, secp256k1, for security. Solving the ECDLP is computationally infeasible, taking an enormous number of operations.
12 words is the best length
12 words is enough.
— Adam Back (@adam3us) March 13, 2023
A 12-word seed phrase provides 128 bits of entropy, aligning with the secp256k1's 128-bit security. The computational difficulty of both brute-force attacks and ECDLP solutions for a 12-word seed phrase is beyond practical reach – billions of years for modern computers.
Longer seed phrases like 24 words don't increase the security of the underlying private keys; they only enhance the resistance against brute-force attacks on the seed phrase itself.
In the realm of hardware wallets, like the Blockstream Jade, you hold the power to choose between a 12-word or a 24-word BIP39 seed phrase, and additionally, you can incorporate a 13th or 25th word for heightened security. This hardware wallet offer innovative features such as SeedQR, a standard introduced by SeedSigner, enabling the encoding of recovery phrases into human-readable QR codes. This functionality simplifies the backup process. Whether you wish to automatically generate a 12 or 24-word seed phrase or prefer the manual approach by adding your unique entropy, the Blockstream Jade caters to your preferences.
A remarkable feature of the Blockstream Jade is its capacity to assist users in generating their seed phrases. Users can input the initial 11 or 23 words of a BIP39 recovery phrase, and the device will diligently compute potential options for the final word. This proves especially valuable for individuals who opt for manual entropy generation, such as rolling dice, in crafting their recovery phrases. This process ensures that valid final word choices are accurately calculated, enhancing the security of the generated seed phrase.
Seizing the opportunity, you can get the Blockstream Jade at an attractive discount using our exclusive coupon code "BLOCKDYOR" (without quotes). Simply follow the link below to explore the Blockstream official store and make the most of this offer, or read our Blockstream Jade Review.
👉 Click here to get the Blockstream Jade. Get a 10% off at checkout with the coupon code BLOCKDYOR.
The Quantum Computing Threat to Bitcoin's Private Keys

The potential of quantum computing has sparked debates about its impact on various technological landscapes, including Bitcoin and the other altcoins' security. Within the Bitcoin community, discussions have emerged regarding the potential risks quantum computing might pose, specifically its ability to crack private keys, a cornerstone of Bitcoin's security.
While quantum computing carries the promise of revolutionizing computational power, the current state of quantum technology and the challenges it faces must be acknowledged. A common sentiment expressed in the Bitcoin community is skepticism about the immediate and widespread impact of quantum computing on Bitcoin's security.
Despite the progress in quantum computing, it remains a monumental task to scale up the number of qubits significantly. This is due to the fragile nature of quantum states, which are described by continuous parameters and are vulnerable to decoherence. The idea that a quantum computer would need at least 1,000 to 100,000 qubits to be useful adds to the complexity of the situation. This far exceeds the number of subatomic particles in the observable universe, highlighting the immense challenge of building and maintaining such devices.
The consensus among experts is that quantum computers could outperform classical ones in specific tasks, but the ability to break cryptographic schemes like SHA-256 remains a formidable challenge. The sheer computational power required for brute-forcing a SHA-256 hash remains beyond the reach of even the most advanced quantum computers envisioned.
The feasibility of quantum computers breaking Bitcoin's security also faces significant limitations. Breaking the Elliptic Curve Digital Signature Algorithm (ECDSA), which is used to generate Bitcoin private keys, is anticipated to be quantum computers' first major achievement. However, many experts dispute the immediacy of this threat, and it is important to note that even if ECDSA were to be compromised, Bitcoin's underlying cryptographic architecture could be adapted to post-quantum cryptography, effectively neutralizing the threat.
Despite the persistent discussions around quantum computing's potential impact on Bitcoin, its practical application remains uncertain and debated within the community. The consensus seems to lean toward a cautious optimism, as experts grapple with the formidable technological hurdles and evolving understanding of quantum computing's true capabilities.
While quantum computing may have the potential to reshape the technological landscape, the idea that it will imminently crack Bitcoin's private keys and disrupt the cryptocurrency market should be met with critical examination. The intricate interplay between quantum computing, cryptography, and the broader blockchain ecosystem is a complex puzzle that continues to be explored, debated, and monitored by the Bitcoin community and technology experts alike.
Bottom line
In the world of Bitcoin and altcoins, the security of private keys forms the bedrock of asset protection. Through intricate mathematical structures, astronomical entropy, and robust hardware solutions, Bitcoin's private keys remain highly secure against even quantum computing threats.
Embracing the strength of well-implemented wallets, verifying entropy, and staying informed about potential vulnerabilities further fortifies the foundation of Bitcoin's security.